Join today and get your first 2 months free.
Fewer criticals, broader coverage, and faster fixes.
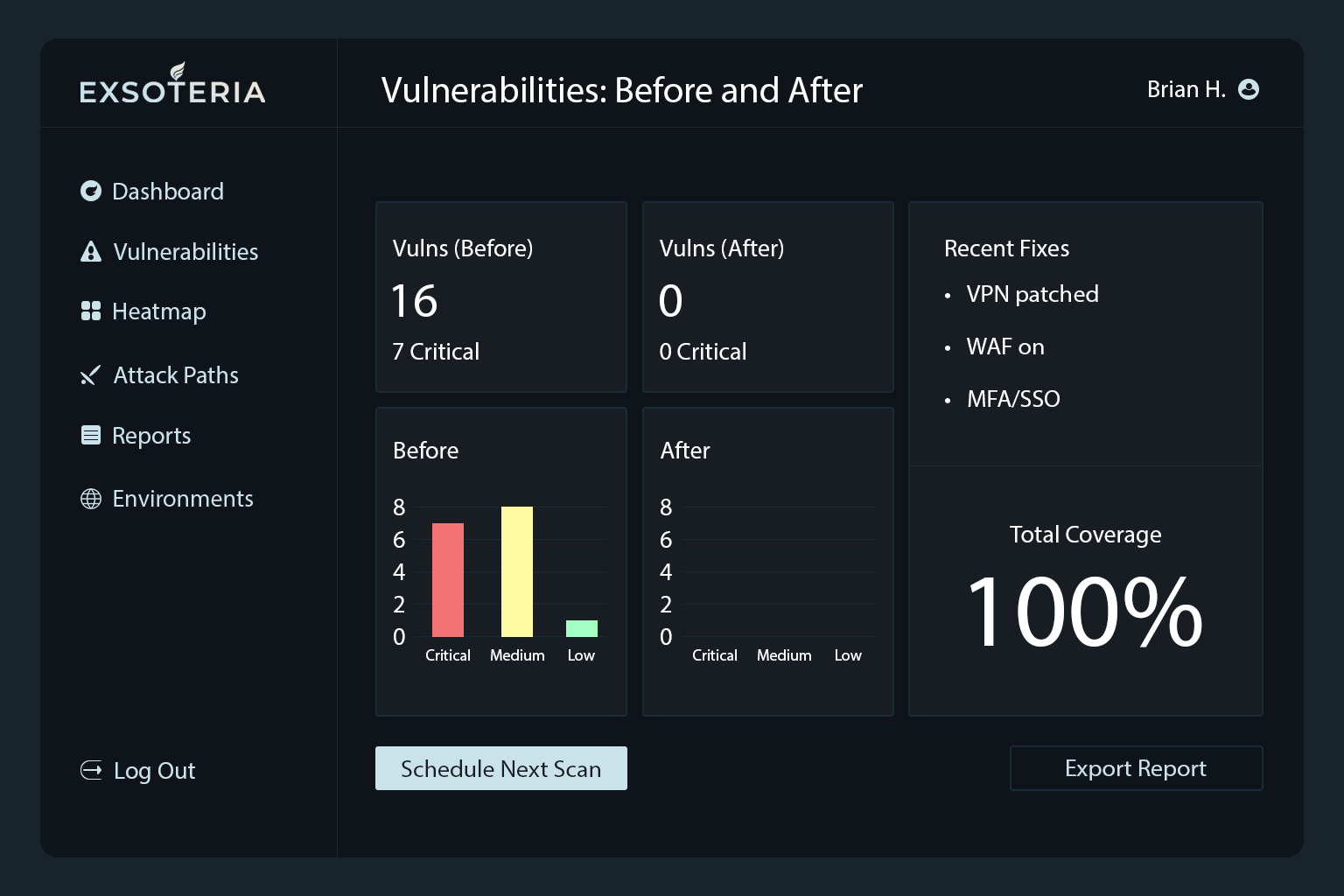
From 7 dangerous flaws to zero, with guided remediation and rapid rescans.
A mid-size SaaS team suspected risk but lacked a clear order of attack. Their first baseline scan surfaced 7 critical issues, including an outdated VPN appliance and a SQL injection in a public-facing app.
Exsoteria prioritized by exploitability and blast radius, showing how a breach could chain from the public site into the admin console. The team patched VPN firmware, added targeted WAF rules, and enforced SSO + MFA for administrative access. We ran auto-rescans after each fix and generated executive summaries for weekly check-ins.
Within 30 days the client reached 0 criticals. High-severity issues trended down and the board got a concise report showing what changed and why it mattered.
Hidden assets surfaced, blind spots closed, and scanning made continuous.
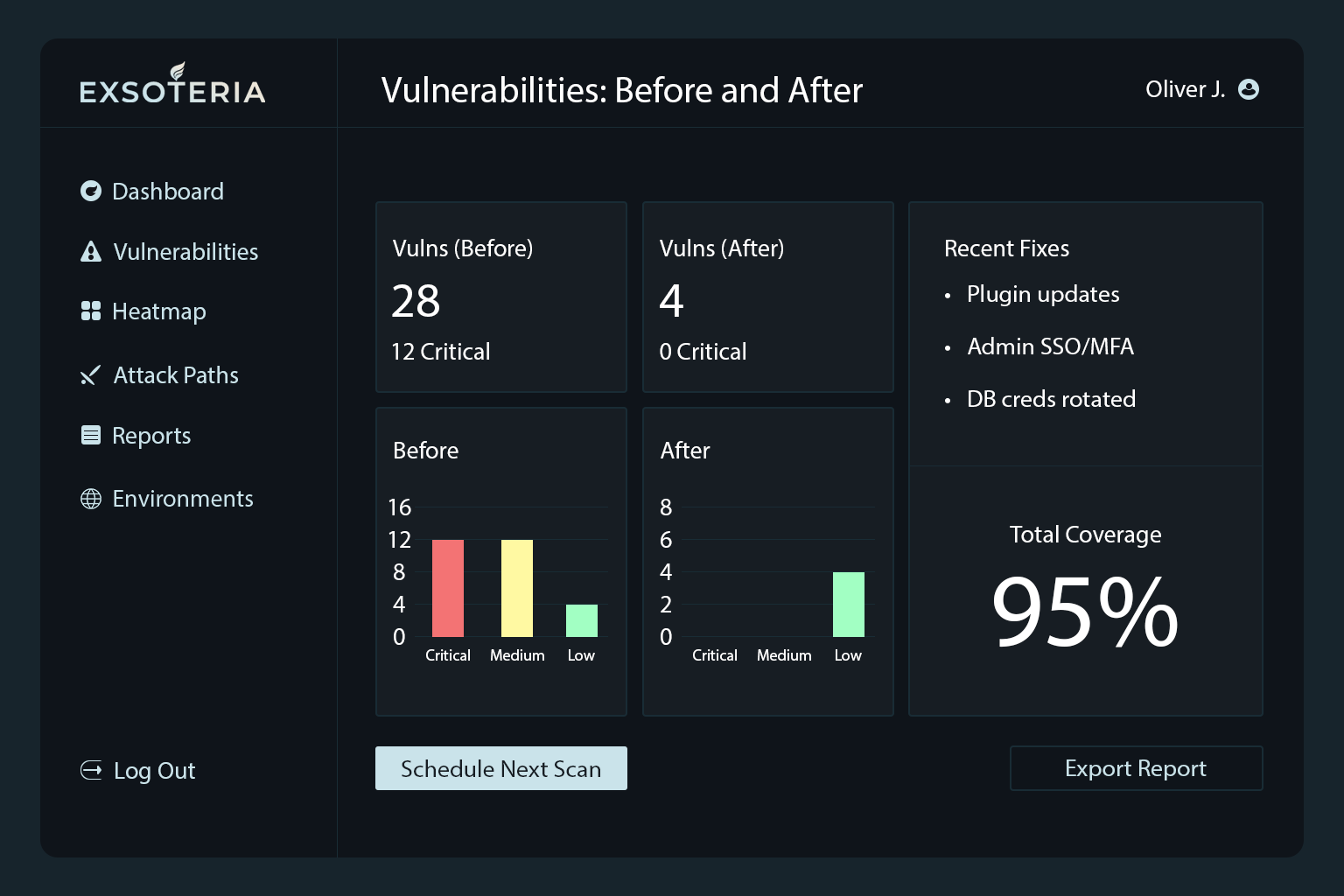
A regional healthcare provider was only focused only on internet-exposed systems, covering about 60% of the real environment. Internal services (legacy app servers, databases, old shares) were effectively invisible to scans—and to auditors.
Exsoteria expanded to internal + external discovery and scanning. We cataloged forgotten hosts, mapped known CVEs and misconfigurations, and grouped issues by impact so teams could fix the right things first. Coverage and risk trended in the Heatmap to keep stakeholders aligned.
Within ~8 weeks, coverage rose to 95% of total assets and audit-blocking gaps were resolved ahead of a compliance review.

Attack path context cut remediation time in half for critical risks.
An e-commerce company’s IT staff struggled with remediation speed. Even when vulnerabilities were identified, critical patches took 4–6 weeks because teams didn’t know which issues mattered most.
Exsoteria’s Attack Path Simulation visualized a realistic chain—VPN → privilege escalation → database—and ranked fixes by the biggest drop in breach likelihood. We routed the top items into Jira/Slack, enforced MFA, and tightened network segmentation.
Mean time to remediation (critical) dropped from ~28 days to under 14 days. Teams finally had a shared, risk-aligned plan—and proof it worked.
Outdated CMS components, exposed tools, and weak creds—prioritized, fixed, verified.
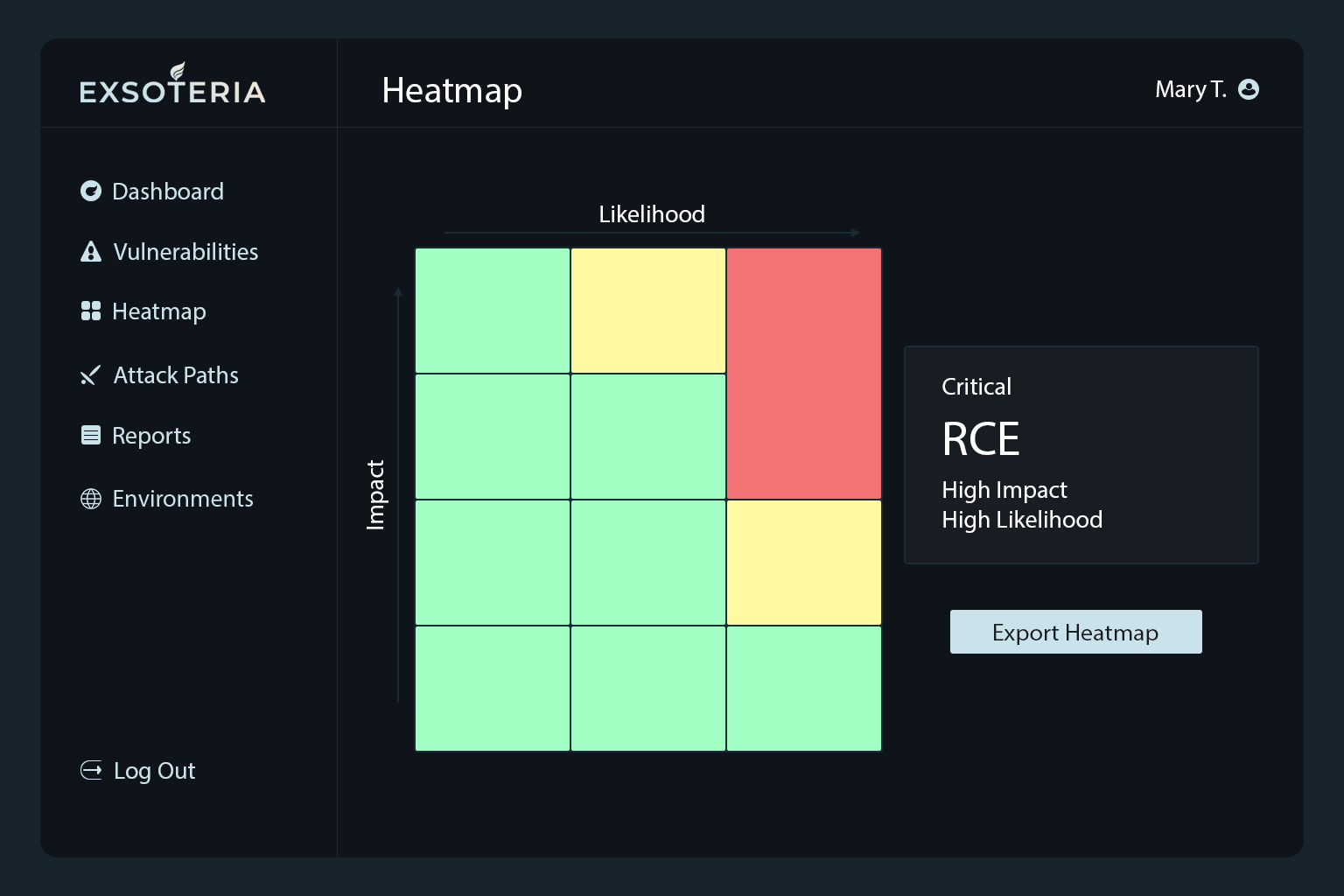
A regional media group ran multiple brand sites on a WordPress/headless stack. The baseline scan surfaced 12 criticals including an RCE-vulnerable plugin, an exposed /admin tool without MFA, and reused database credentials between staging and production—made riskier by legacy plugins and a fast publishing cadence.
We started with a full plugin/theme audit, removing or pinning the vulnerable plugin and tightening supply-chain controls. The /admin surface moved behind SSO + MFA with VPN/IP allowlisting, and a light WAF ruleset blocked common WordPress payloads without breaking CDN or cache behavior. Secrets were split by environment, database credentials were rotated, and shared accounts were retired. Every change triggered an auto-rescan and a short verification note aligned to the editorial release schedule.
Within 21 days the team reached zero criticals with no publishing downtime. Over the following two weeks, high-severity items fell from 19 to 6. Auto-rescans verified fixes within 24 hours, and the organization left with a gated admin surface, per-environment secrets, and a tracked plugin list ready for future audits.
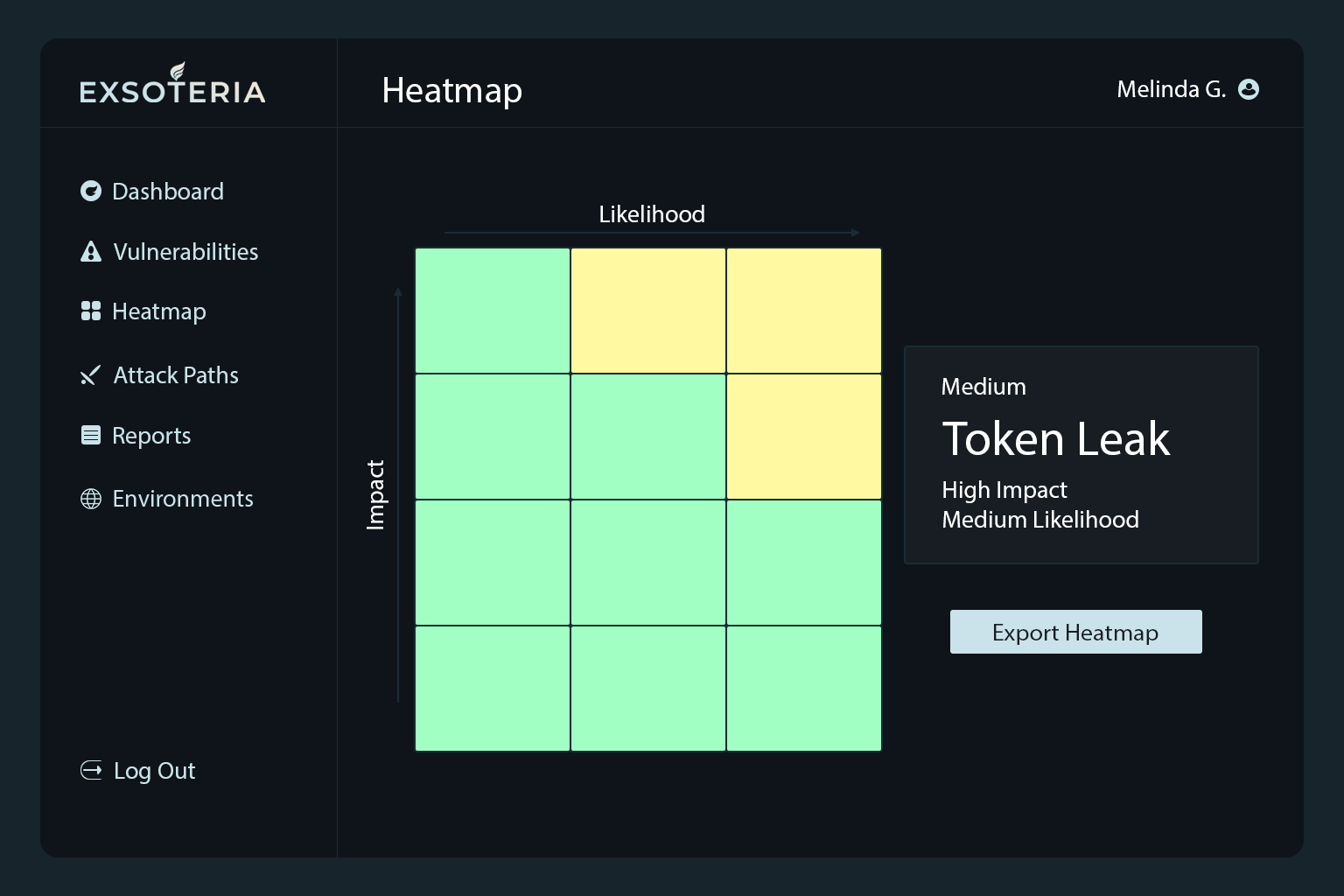
Secret exposure in CI/CD mapped to an exploit chain and cut off at the source.
A fintech API company discovered an NPM access token in a public repo. Attack Path Simulation showed a credible chain—Git → CI runner → staging app → shared DB creds → production read—and leadership needed to cut revoke time and block lateral movement.
We revoked the token immediately, purged it from git history, and invalidated CI caches. The pipeline moved to short-lived OIDC tokens; database credentials were rotated and staging/production roles were separated. GitHub secret scanning, branch protection, and required reviews were enabled. CI runners lost broad egress and were reduced to least-privileged scopes. Publishing now requires SSO with step-up MFA and org-wide 2FA on NPM. Finally, build guardrails fail on secret detection, alert SecOps in Slack, and stream evidence into the SIEM.
The modeled attack-path risk dropped from 8.8 to 4.1 as lateral movement was cut off by split credentials and network restrictions. Secret-revoke time fell from about six hours to 45 minutes thanks to the new playbook and alerts, and an attempted token reuse a week later was blocked at authentication. The team recorded zero unauthorized publishes and gained clean, exportable audit evidence.